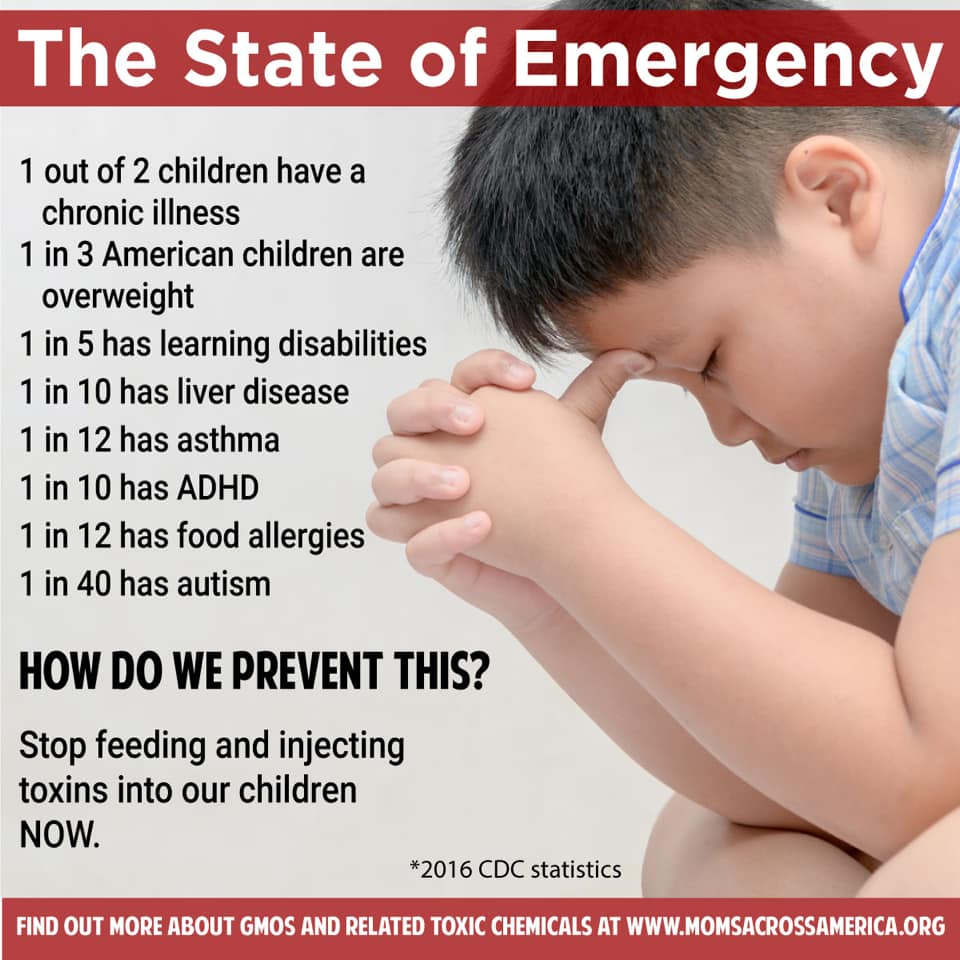
Here is a very genuine state of emergency which the big pHarma funded legislators do not even acknowledge let alone address!

Tom's Blog on Life and Livingness
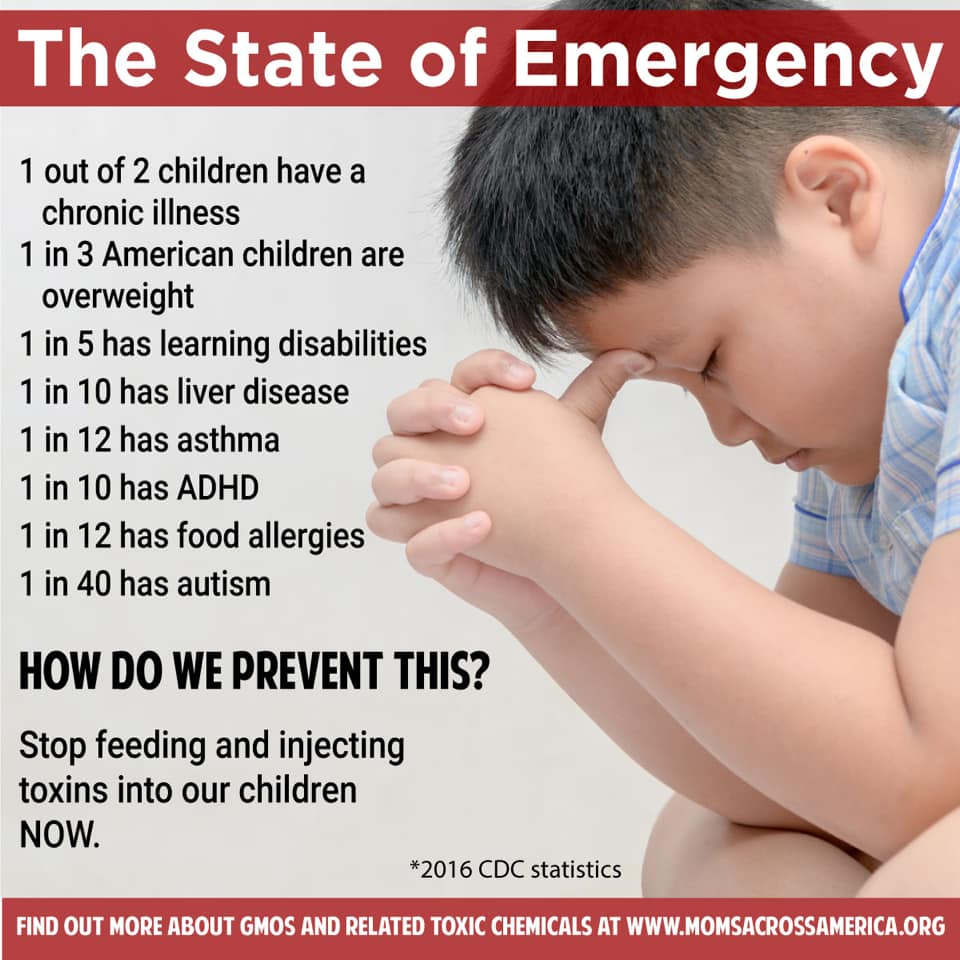
Here is a very genuine state of emergency which the big pHarma funded legislators do not even acknowledge let alone address!
I was sent a Glossary of SEO Terms that I thought you might find useful:
http://netvantagemarketing.com/blog/seo-glossary
Is Overpersonalisation Killing the Variety and Interest of Your User Experience?
One user even noted that because the content was boring she continued to scroll looking for something that was interesting, “I don’t find anything interesting on Facebook tonight but what’s funny is that I will keep scrolling until I do; it’s addicting.” This behavior is related to the Vortex phenomenon, which refers to people feeling sucked into the online world almost against their will through sticky design techniques (like continuous content feeds). Users seek the emotional payoff they get from a good piece of content. In these cases, the phone turns into a mini slot machine: they keep pulling the lever coming across dozens of losers in hopes of finally getting a winner.
A file naming decision harkening back to the earliest days of personal computing is still very much alive in Microsoft’s Windows 10 and its Azure Functions serverless cloud code execution tool, much to the merriment of geeks old enough to remember the reasons for it.
https://www.itnews.com.au/news/how-a-1974-bug-still-bites-win10-and-azure-users-515102
Summary: Usability testing finds that both voice-only and screen-based intelligent assistants work well only for very limited, simple queries that have fairly simple, short answers. Users have difficulty with anything else.
https://www.nngroup.com/articles/intelligent-assistant-usability/

Another reason why I do not trust putting all my data on someone else’s cloud service.
https://www.itnews.com.au/news/eight-more-spectre-style-flaws-found-in-intel-processors-490279
The security of pretty much every computer on the planet has just gotten a lot worse, and the only real solution — which of course is not a solution — is to throw them all away and buy new ones.
On January 3, researchers announced a series of major security vulnerabilities in the microprocessors at the heart of the world’s computers for the past 15-20 years. They’ve been named Spectre and Meltdown, and they have to do with manipulating different ways processors optimize performance by rearranging the order of instructions or performing different instructions in parallel. An attacker who controls one process on a system can use the vulnerabilities to steal secrets elsewhere on the computer.
This means that a malicious app on your phone could steal data from your other apps. Or a malicious program on your computer — maybe one running in a browser window from that sketchy site you’re visiting, or as a result of a phishing attack — can steal data elsewhere on your machine. Cloud services, which often share machines amongst several customers, are especially vulnerable. This affects corporate applications running on cloud infrastructure, and end-user cloud applications like Google Drive. Someone can run a process in the cloud and steal data from every other user on the same hardware.
I am sure people thought me weird and old fashioned because I would not subscribe to the Cloud philosophy. This is exactly one reason why. – Tom)
Information about these flaws has been secretly circulating amongst the major IT companies for months as they researched the ramifications and coordinated updates. The details were supposed to be released next week, but the story broke early and everyone is scrambling. By now all the major cloud vendors have patched their systems against the vulnerabilities that can be patched against.
https://www.schneier.com/crypto-gram/archives/2018/0115.html

If you have a web page, worth reading…
http://www.sitepronews.com/2018/01/08/4-ways-google-changing-search-engine-results/
Well, UX (User eXperience) is a field set to really take off!
https://www.nngroup.com/articles/100-years-ux/
The recent Equifax Cybersecurity Breach was an eye opener like no other. The personal information of 145 million Americans were taken, including but not limited to social security numbers, addresses, and credit card numbers. This means that some enterprising and unscrupulous individuals have access to confidential data — and were able to accomplish this with relative ease. In light of this, cybersecurity experts have put out a number of helpful tips to help you maintain your safety online.
Use special passwords:
As much as possible, avoid birthdays, chronological number sequences, literary quotes, and popular song lyrics. According to News.USF.edu, hackers have software to guess and crack passwords in seconds. Instead, use phrases or statements known only to you (“The chair is against the wall”), or the first letters of each word in those statements (“tciatw”).
Don’t use the same password more than once:
Utilizing duplicate passwords for multiple accounts make it easier for hackers to enter these accounts.
Change passwords every six months:
Though this seems tedious, switching up your passwords can make a world of difference.
Avoid clicking on links in emails and opening attachments:
Ensure first that the emails are authentic, meaning that they don’t come from trick email addresses (e.g. “lotsamoney.com”). To check if links are safe, just hover your cursor over them. Doing this will show the address. In line with this, steer clear of any ads or apps in these emails.
Be wary of apps:
If you really must download apps, do so from the app store for your operating system. And before you install them, check to see if they won’t be accessing unnecessary information (e.g. a drawing app doesn’t need to see your contacts list).
Use secure networks:
If you can, avoid using public WiFi networks. They may be convenient, but they’re not secure. Connecting to public WiFi leaves you vulnerable and exposed to any hackers keeping an eye on that particular network. (Related: Software security group demonstrates how hackers can use ransomware to harm and potentially kill hospital patients.)
Keep up to date with security measures:
Make use of antivirus software and ensure that it’s up to date, and make it a point to do the same for any security features your browser and operating system may have. This will give you a much-needed extra layer of protection whenever you’re online. In addition, choose multi-factor authorization. It’s an extra bit of work but totally worth it, since a second level of verification can notify you if and when someone is attempting to hack into your account.
Look for the lock:
Specifically, the little green padlock before the website URL in the web address bar. The padlock serves as an indication to let you know that your login and account information is encrypted and won’t fall victim to unauthorized access.
https://nexusnewsfeed.com/article/science-futures/simple-steps-for-preventing-your-online-presence-from-being-hacked/