This article reports survey results for a specific design factor for web sites. Usefulk if you have anything to do with specifying design elements for a web site.
Complex Application Design: A 5-Layer Framework
An interesting article on the various contexts of complexity that should be considered by user experience designers and researchers designing complex applications, including complexities of integration, information, intention, environment, and institution.
https://www.nngroup.com/articles/complex-application-design-framework/
We Got Hacked
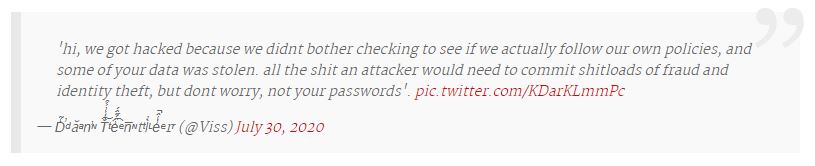
US bank Morgan Stanley has posted letters to an unknown amount of customers, notifying them of potential data breaches involving sensitive personal information left on servers and storage sent to recyclers and on an encrypted drive lost at a branch office.
(Tom: In my personal opinion, having my info in the hands of banks and others with whom I do business is risky enough, as this story illustrates only too well, but storing personal or business data in the cloud takes the risk of loss to a whole new level. That is why I continue to use the accounting and business software I created myself hosted on an inhouse computer.
As an additional note, ransomware, phishing and hacking scams are costing businesses obscene amounts of money. Travel giant CWT pays $6.3m ransom to cyber criminals https://www.itnews.com.au/news/travel-giant-cwt-pays-63m-ransom-to-cyber-criminals-551133
Do some homework and formulate firm policy with which you (and any staff) deal with your emails and web sites you visit. For instance I:
Use strong malware protection, currently Emisoft Enterprise Security Suite.
Never click on links in an email from unknown senders.
Even from known senders I sometimes receive emails with just a link, no explanatory text. I do not click on those. I will sometimes email the sender to ask what it is about.
Never download from file transfer sites unless I expect a link from that person and
Always check the displayed and hidden URL match the expected domain as miscreants will sometimes use what is called a sub-domain or sub-folder to make it look more legitimate. For instance last week I got one allegedly from wetransfer.com but when I held my mouse over the link it was not the wetransfer.com domain, that was used as a folder name like this:
www.somethingelse.com/wetransfer/qweoxflkwefow
A valid name used as a sub-domain for a hacker site looks like this:
wetransfer.hackerdomain.com/as/dkfjswlk
So, just because it has a recognisable name somewhere in the URL, that is a trick to fool those not fully tech savvy. Now you are informed, don’t fall for it.)
https://www.itnews.com.au/news/morgan-stanley-customer-data-left-on-decommissioned-servers-551094
Good Abandonment on Search Results Pages
If you have a web site this might be of interest to you.
Just-Right Personas: How to Choose the Scope of Your Personas
A “Persona” is a fictional representation of an actual user and is applied in the early stages of product development or product redesign. Personas are vital to the success of a product because they drive design decisions by taking common user needs and bringing them to the forefront of planning before design has actually started. Personas provide the team with a shared understanding of users in terms of goals and capabilities. Once Personas are defined, going through a task analysis exercise with scenarios will offer an inexpensive way to test and prioritize features throughout the development (see lesson #2 in the blog Responsive Design: Getting started).
Narrow and broad-scope personas achieve different goals. Success depends upon knowing the tradeoffs and structuring your personas’ scope based on what you are trying to achieve. (7 min. to read) https://www.nngroup.com/articles/persona-scope/
Variations on Practiced Patterns Cause Mistakes
We all build habits based on where on the screen standard User Interface elements are placed. Deviating from those placements means we cannot use our trained habit patterns and when we do as we habitually do, we make mistakes.
https://www.nngroup.com/articles/practiced-patterns-mistakes/
A Useful Tool If Your Email Account Is Blacklisted
Small Pictures on Big Screens: Scaling Up from Mobile to Desktop
If you manage a web site that has images needing to be viewed on small and large screens this is useful data.
https://www.nngroup.com/articles/small-pictures-big-screens/
Guide to Online Privacy
Some interesting data here too!
https://www.vpnmentor.com/blog/ultimate-guide-online-privacy/
Beyond Usability: 3 User Experiences Reshaping Their Industries
Rent the Runway, Uber, and Airbnb challenge the traditional experiences of their industries. (10 min. to read)
https://www.nngroup.com/articles/3-user-experiences-reshaping-industries/
